Search
Items tagged with: Mastodon
Echte Admin-Accounts erkennt man an einem speziellen Rollen-Badge im Profil – allerdings in der Regel nur, wenn man sich online im Browser einloggt.
Guide for Using Mastodon Search: It’s Easier and More Powerful Than You Might Think
Content warning: [img=https://i.snap.as/UCwlKrUe.png]The Mastodon logo with an illustration of a cute mastodon that's smiling with its eyes squinting in delight. It’s holding a mobile device and looking off to the side. A search form input is overlaid with placeholder tex
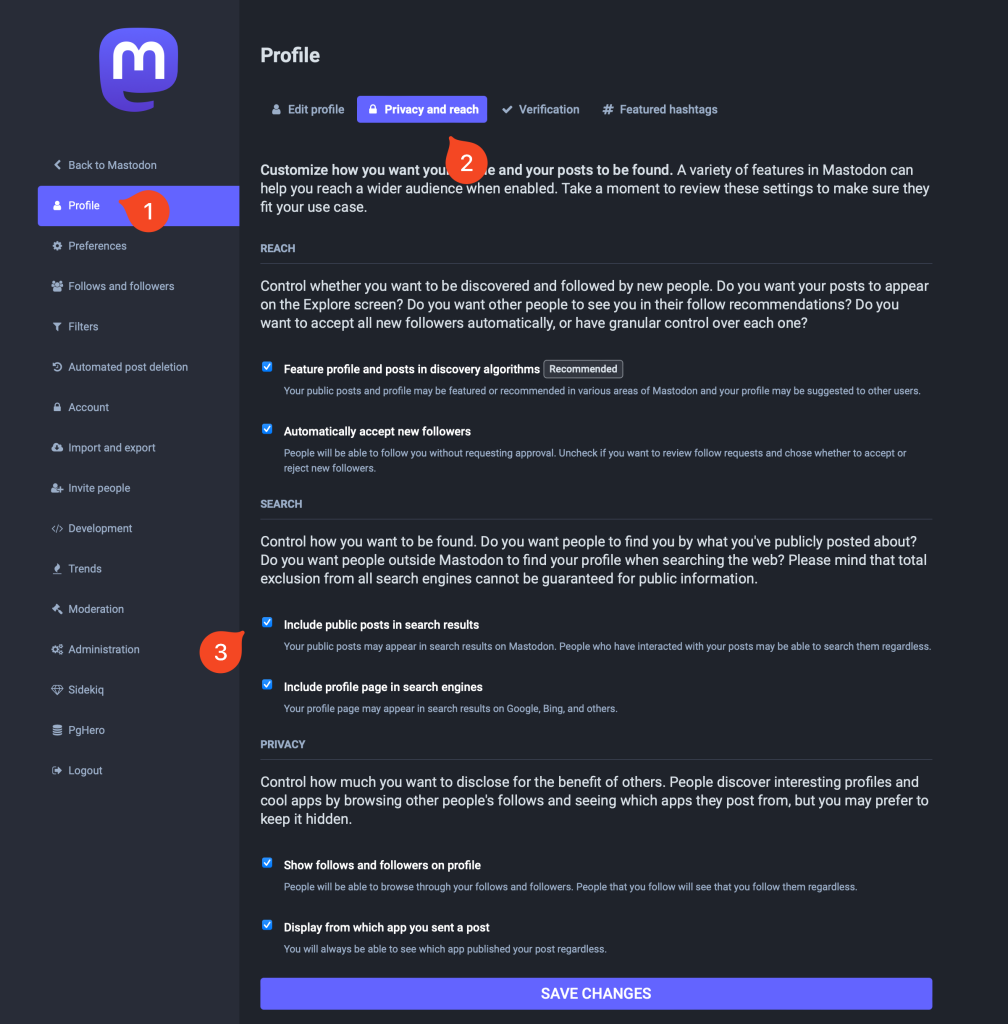
Full text search has been merged in #Mastodon `main` branch, and will be in the next (and final?) 4.2.0 beta 🎉
It is opt-in, so it will take some time to be filled with people content as they enable their profile to be indexed, but this was one of the most wanted Mastodon features for some time.
We plan to deploy it to mastodon.social and mastodon.online in the coming days to have a bit more feedback on it and see how it behaves in the wild.
Some words about Mastodon moderation:
1. It’s hard. No decision is easy and there’s lots of gray area even with explicit rules.
2. We’ll sometimes debate for a long time on a single post. We do our best to make the right call.
3. Even so, we sometimes make mistakes. We’re willing to accept appeals when that happens.
4. We get a lot of things right. You can’t even imagine some of the traumatic things we see.
1/5
#Mastodon #Moderation #Admin #Kindness #Empathy #Hate #Safety #MastoAdmin
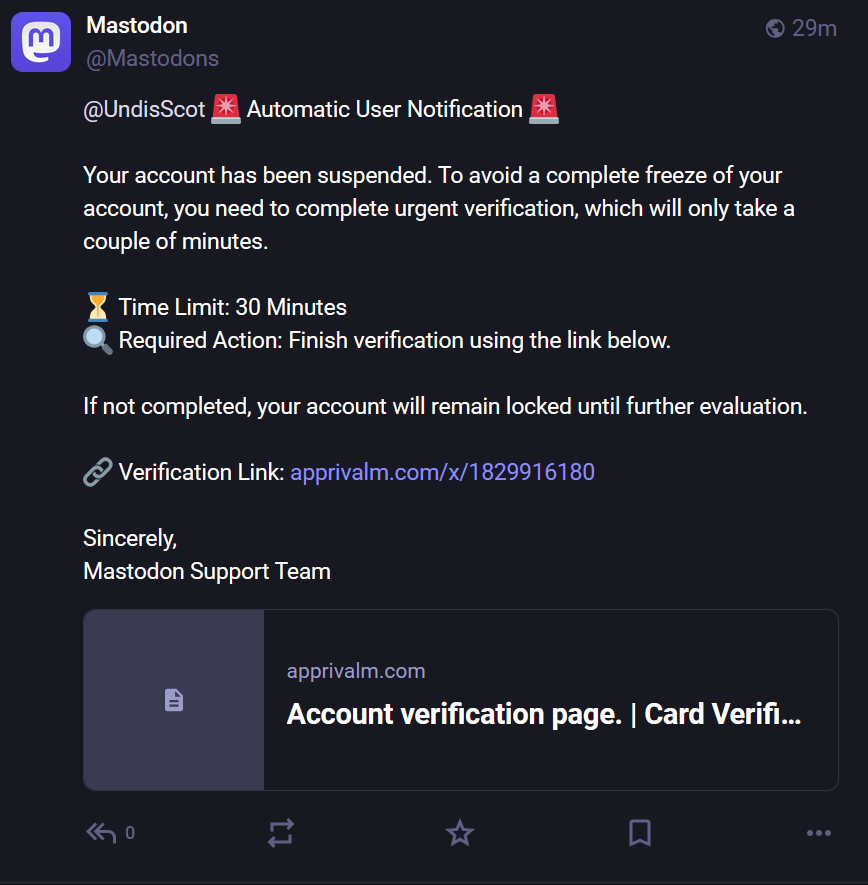
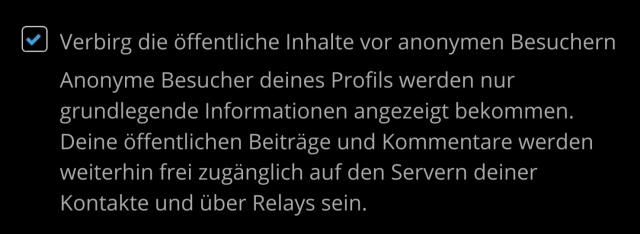
ALERT for Bluesky Bridge Users 🚨 🦋
If you are using a Bluesky bridge on Mastodon, DO NOT TAG Mastodon accounts in your posts without prior informed consent from this person.
This could end up showing a preview of this person's profile picture and bio on Bluesky without their consent.
Additionally, be careful about how the upcoming Quote Post feature could behave with Bluesky bridges.
Some of us don't want our information shared with commercial platforms like Bluesky, and have not consented to this bridge.
This practice can even endanger some Fediverse users.
If you have chosen to share your
own data with commercial platforms, make sure you leave the same choice to others.
This is important.
#Privacy #Mastodon #Bluesky #BlueskyBridge #Fediverse #Consent
After 2 years I managed to get WebApe to the official list of Mastodon providers https://docs.joinmastodon.org/user/run-your-own/
In order to support the so many free projects we are doing, we are also trying to provide hosting and management for Mastodon, Friendica and the like.
For those interested see https://webape.site/
Basically if you need a Mastodon instance, or Peertube, or Friendica and so forth, you pay a monthly fee and we do everything. No need to worry about updates and all that.
Mastodon get your stuff together and remove any arbitration clause.
https://github.com/mastodon/mastodon/issues/35086
#mastodon #arbitration #law #IP
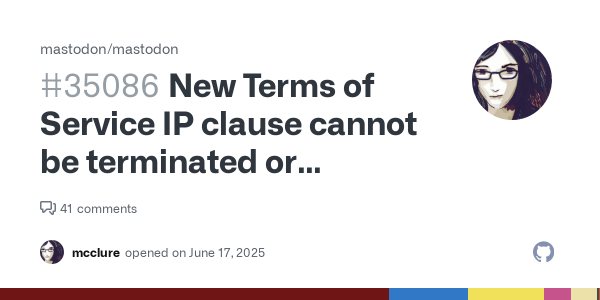
New Terms of Service IP clause cannot be terminated or revoked, not even by deleting content
Summary Since it first opened, mastodon.social has operated without any sort of explicit IP grant from the users to the service, which is unusual for a social networking service. Today Mastodon ann...mcclure (GitHub)
Just moved from fosstodon to fediscience.
This is the third time I've moved #Mastodon instances! I've never wanted to move, but there have been compelling reasons each time.
I am always impressed at how seamless it has been every time I have moved instances.
I have 2 Friendica accounts and 1 on Mastodon. Both Friendica accounts are following the Mastodon one. If i like or share a posting of the #Mastodon account out of my Friendica timelines, these are acknowledged and counted on the Mastodon account. But only one of the #Friendica accounts triggers a notification on Mastodon, the other doesn't.
How can this be?
-----
"Optimismus ist nur ein Mangel an Information." (Heiner Müller)
♲ NABU Jena - 2025-05-26 13:27:19 GMT
Juhu 🎉
Der #NABU hat nun seine eigene, offizielle Fediverse-Instanz. Als NABU-Jena hatten wir die Ehre, den Umzug zu testen. In Zukunft werdet ihr hoffentlich viele unserer Verbände hier wiederfinden.
#Mastodon #Fediverse #Jena #Unabhängikeit #OpenSource
I want to give #Mastodon a proper go this time, but it's hard to connect with people when no-one follows you, and hashtags only get you so far. 😞
So, if you like one of the hashtags below, please consider following me, and if you do, I'll follow you back! Thank you. 💗
#retrocomputing #msdos #windows #vintagecomputing #ai #lego #scifi #amiga #linux #doctorwho #drwho #startrek #starwars #space #uk #lgbtq #3dprinting #woodworking #discworld #reading
Am 6. Mai veranstalten wir gemeinsam mit @wikimediaDE und dem @bmuv den online-Workshop
🥁 🥁 Das #Fediverse und seine sozialen Medien.
Mit @nic, @melaniebartos, @MoniKa, @digitalcourage, @cyber4EDU, und @RoedigerRG wird das dezentrale Netzwerk 🕸️ vorgestellt und ganz praktisch in die Nutzung von #Mastodon, #PeerTube und #Pixelfeld eingeführt.
Anmeldung hier
👉 https://www.bmuv.de/veranstaltung/teil-1-der-workshopreihe-sovereign-sustainable-digital-das-fediverse-und-seine-sozialen-medien

Teil 1 der Workshopreihe Sovereign. Sustainable. Digital.: Das Fediverse und seine sozialen Medien- BMUV - Veranstaltung
In diesem interaktiven Online-Workshop wird das Fediverse vorgestellt - ein dezentrales Netzwerk, das community-basierte soziale Plattformen wie Mastodon, PeerTube und Pixelfeld umfasst.Bundesministerium für Umwelt, Naturschutz, nukleare Sicherheit und Verbraucherschutz
#Fellowship in Kooperation mit dem SWR X Lab und Mastodon
Das #SWR X Lab untersucht die Potenziale des #Fediverse für den öffentlich-rechtlichen Journalismus.
In Kooperation mit dem Media Lab Bayern und der Tech-Plattform #Mastodon wurde dazu ein Fellowship entwickelt.
Ziel ist es, innovative Lösungsansätze für sechs definierte Herausforderungen im Umgang mit ActivityPub zu finden.
https://www.media-lab.de/de/angebote/reinvent-social-platforms/#fellowship-in-kooperation-mit-dem-swr-x-lab-und-mastodon
#ÖRRbewegen #SWRX #MediaLabBayern #ActivityPub #ÖRR #Journalismus

Förderung in Kooperation mit dem SWR X LAB und Mastodon
★ 10.000 € Förderung ★ 6 Monate ► Finde neue Lösungsansätze für soziale Plattformen und entwickle mit anderen Expert:innen funktionierende Prototypen.Media Lab Bayern
Is there an account you follow that boosts other people too much? Do you like reading their own posts, but you don't want to see their boosts?
In Mastodon you can hide an account's boosts by doing the following:
1. Go to their profile page
2. Click the ⋯ button on their profile
3. Select "Hide boosts"
You will still see their posts, it will only hide boosts. If you change your mind, go to ⋯ and select "Show boosts".
They will never know you have hidden their boosts 🙂
Why we currently do not recommend the @rodentapp Mastodon client:
- it's not #opensource let alone #FLOSS
- it's only available from Google's Play store
- it contains trackers (Google Crashlytics and Google Firebase Analytics)
- it wants access to your ad ID
In short, this app is against the spirit of Mastodon and the Fediverse. There are plenty of Mastodon apps that respect you: @Tusky, Fedilab (@apps), @moshidon …
#Mastodon #Rodent #Android #App #AlternativeTo #Alternative

Report for social.rodent 1.28.0
Known trackers, permissions and informations about this specific version of this applicationεxodus
Ich habe gerade den "Leitfaden für den Instanz-Betrieb im dezentralen Netzwerk - Datenschutz bei Mastodon" von gefunden.
Dieser gibt neben grundsätzlichen Informationen auf was Instanzbetreiber achten müssen, vor allem auch eine sehr praktische Sammlung an Musterdokumenten unter CC BY-ND 4.0-Lizenz. Ihr könnt es also für euere Instanzen anpassen und nutzen.
Auch relevant für @Friendica Admins / @Friendica Support
Auf einem abstrakten Niveau sind die Anforderungen, die wir beschreiben, auch auf andere Plattformen des Fediverse übertragbar. Dennoch gibt es einige Aspekte, die von der konkreten Plattform und Software-Implementierung abhängen. So sind zum Beispiel die Möglichkeiten, rechtliche Texte einzubinden und anzuzeigen, unterschiedlich.
Danke@DS_Stiftung@social.bund.de
https://stiftungdatenschutz.org/praxisthemen/datenschutz-bei-mastodon
#impressum #dsgvo #fediverse #friendica #mastodon #tos #deutschland #datenschutz

Praktische Umsetzung und Musterdokumente
Die Stiftung Datenschutz wurde im Januar 2013 von der Bundesrepublik Deutschland als Stiftung privaten Rechts gegründet. Sie ist gemeinnützig und verfolgt keine gewerblichen Interessen.stiftungdatenschutz.org
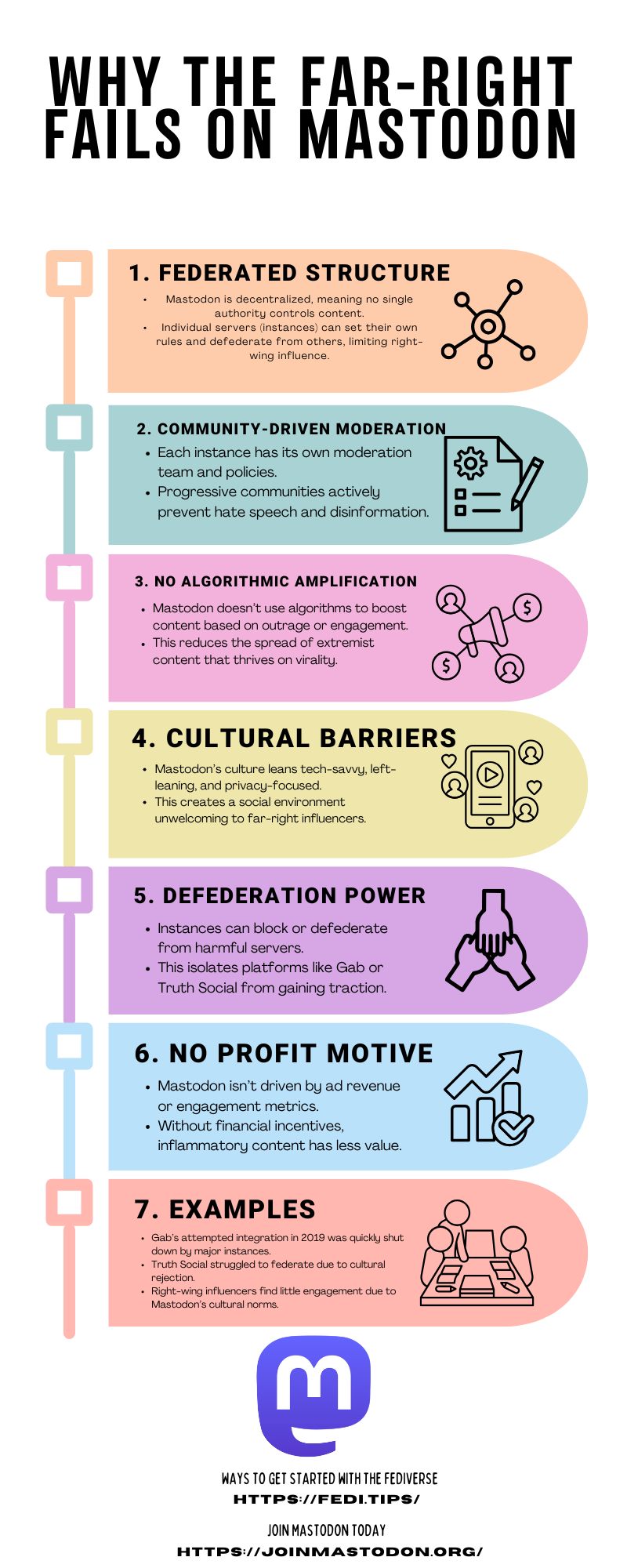
So a short infographic I've been working based on the talks I've had over the weekend and when the 5 cups of coffee finally left my body.
The default character limit should be 5,000 rather than 500 · Issue #34125 · mastodon/mastodon
Pitch Mastodon currently has a default character limit of 500. People are always looking for instances with a higher character limit count, and others see the current 500 character limit as limitin...GitHub
🎉 Die heutige Fediverse-Sprechstunde ist zu Ende.
Ein herzliches Dankeschön geht an Tobias tobias@social.diekershoff.de für seine Ausführungen zu #Friendica ! Wir hatten eine spannende Runde mit vielseitigen Themen, die sowohl für #neuhier als auch für fortgeschrittene Nutzer interessant waren. Im Fokus standen heute Anwendungen im #Fediverse, insbesondere zu Friendica. Mein Dank gilt auch allen Teilnehmenden der Sprechstunde, die sich aktiv eingebracht und so erneut zu einer gelungenen Veranstaltung beigetragen haben.
Diesmal haben wir den Vortrag von Tobias aufgezeichnet. Der Link kommt morgen.
🗓️ Der nächste Termin steht bereits fest: Donnerstag 27.03.2025 um 19:30 Uhr
Weitere Details folgen.
✨ Fediverse-Sprechstunde – Mach mit! ✨
📅 Donnerstag, 27.02.2025 – 19:30 Uhr (Online)
Hast du ein spannendes Thema oder möchtest du deine Erfahrungen im Fediverse teilen? Dann sei dabei! Wir suchen noch Vortragende und Themen, die unsere nächste Fediverse-Sprechstunde bereichern.
💡 Für Einsteiger: Du bist neu hier? Kein Problem! Wir helfen dir beim Einstieg: Profil einrichten, Sicherheitstipps, Posten & Vernetzen.
🌍 Für Erfahrene: Du nutzt bereits Mastodon, Hubzilla, Friendica, Pixelfed, Misskey oder andere Anwendungen? Dann teile dein Wissen mit der Community!
🔗 Gemeinsam lernen, entdecken und vernetzen – sei dabei!
#Fediverse #Mastodon #Friendica #Pixelfed #Misskey #FediverseSprechstunde
Hi there @utopiarte,
I'm observing this #poll question on the #friendica @helpers #group from over here on a #mastodon instance and can't like, only fav, yet actually I'd like to be against this proposal as it is very dangerous!
I wouldn't put my name on the line in this internet for poll's by name vote, #democracy or even post an opinion.
That's way to dangerous in the actually #zeitGeist of #neoLiberalFascist's having the thumb on LLM's to hunt us down.
https://www.youtube.com/watch?v=mxNZduzm6B8
Grüss mir die Genossen
Provided to YouTube by WM GermanyGrüss mir die Genossen · WesternhagenMit Pfefferminz bin ich dein Prinz℗ 1978 WEA RECORDS / WARNER MUSIC GERMANYDrums: Jean ...YouTube
"the Mastodon in the room"
— @matt
#FOSDEM #FOSDEM2025 #SocialWebFOSDEM #Fediverse #Mastodon #WriteFreely
Nice. How to leave #X / #Twitter and #Instagram? In the edition of tomorrow‘s newspaper Augsburger Allgemeine offers valuable tips and highlights alternatives in the #Fediverse, such as #Mastodon and #Pixelfed.
A must-read especially for @Gargron from @Mastodon and @dansup from @PixelFed and of course @helpers / @admins
📖 Read more here in german language: https://www.augsburger-allgemeine.de/geld-leben/social-media-alternativen-bluesky-signal-co-neustart-ohne-x-und-meta-104511246
#SocialMedia #Privacy #Alternatives #Mastodon #Pixelfed #Fediverse

Social-Media-Alternativen: Bluesky, Signal & Co: Neustart ohne X und Meta
Sie hadern mit Elon Musks Kurznachrichtendienst X und sind auch nicht mehr glücklich mit all dem, was Mark Zuckerbergs Meta-Konzern anbietet? Kein Problem. Es gibt Alternativen.Von Dirk Averesch, dpa (Augsburger Allgemeine)
Nice. How to leave #X / #Twitter and #Instagram? In the edition of tomorrow‘s newspaper Augsburger Allgemeine offers valuable tips and highlights alternatives in the #Fediverse, such as #Mastodon and #Pixelfed. A must-read especially for @Gargron from @Mastodon and @dansup from @PixelFed and of course @helpers / @admins
📖 Read more here in german language: https://www.augsburger-allgemeine.de/geld-leben/social-media-alternativen-bluesky-signal-co-neustart-ohne-x-und-meta-104511246
#SocialMedia #Privacy #Alternatives #Mastodon #Pixelfed #Fediverse
Social-Media-Alternativen: Bluesky, Signal & Co: Neustart ohne X und Meta
Sie hadern mit Elon Musks Kurznachrichtendienst X und sind auch nicht mehr glücklich mit all dem, was Mark Zuckerbergs Meta-Konzern anbietet? Kein Problem. Es gibt Alternativen.Von Dirk Averesch, dpa (Augsburger Allgemeine)
[strong]Friendica: Wie erstelle ich noch mal eine Content Warning für Mastodon User?[/strong]
Wie kann ich auf Friendica noch mal eine CW für Mastodon User erstellen?
#Friendica #Frage #ContentWarning #CW #Mastodon #2025-01-28 !Friendica Support
When I opened up Lemmy this morning I could not believe my eyes. The top story was a headline from Forbes stating:
« ‘Open Source And Ethical’ TikTok, WhatsApp And Instagram Alternatives Could Transform Social Media ».
The article mostly focused on #Pixelfed and did a fairly good job explaining how #ActivityPub works. But they spelled #Mastodon « Mastadon » over and over again with no links to it. Yikes.
B for the effort, but please editors do better!

‘Open Source And Ethical’ TikTok, WhatsApp And Instagram Alternatives Could Transform Social Media
As major platforms face mounting scrutiny over content moderation and user privacy, a developer's vision for ethical social media draws supportEsat Dedezade (Forbes)


 I’m Mark Wyner, an activist, dad, husband,
I’m Mark Wyner, an activist, dad, husband, 
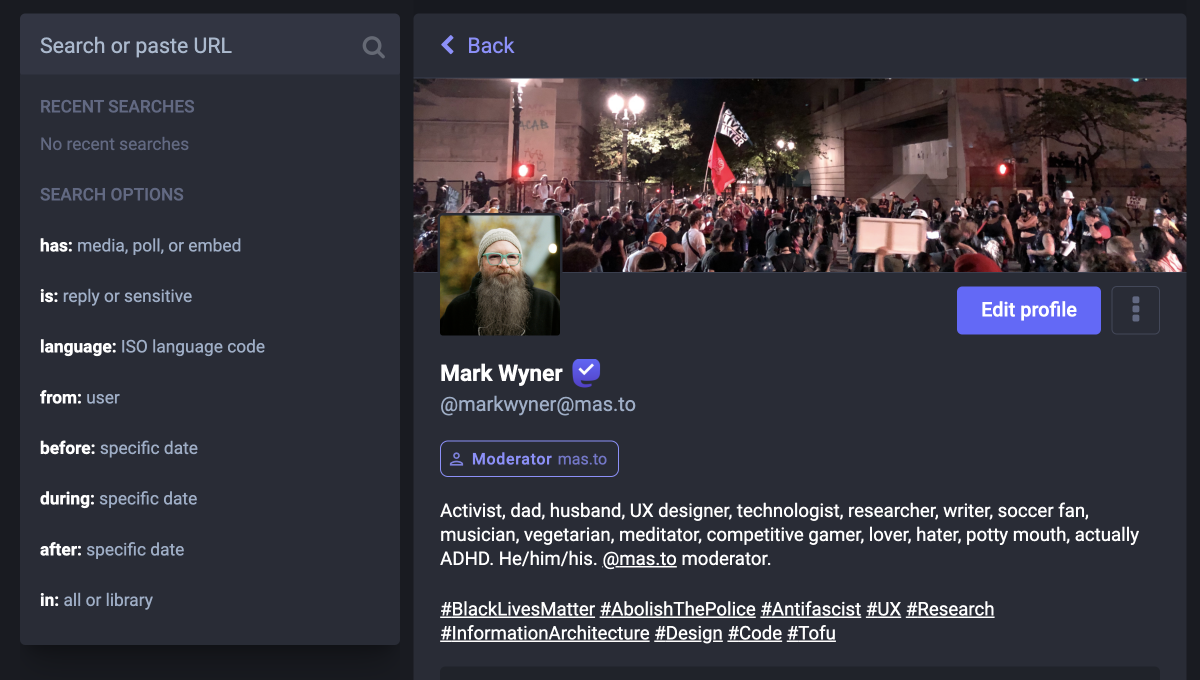 Fig 1: search anatomy
Fig 1: search anatomy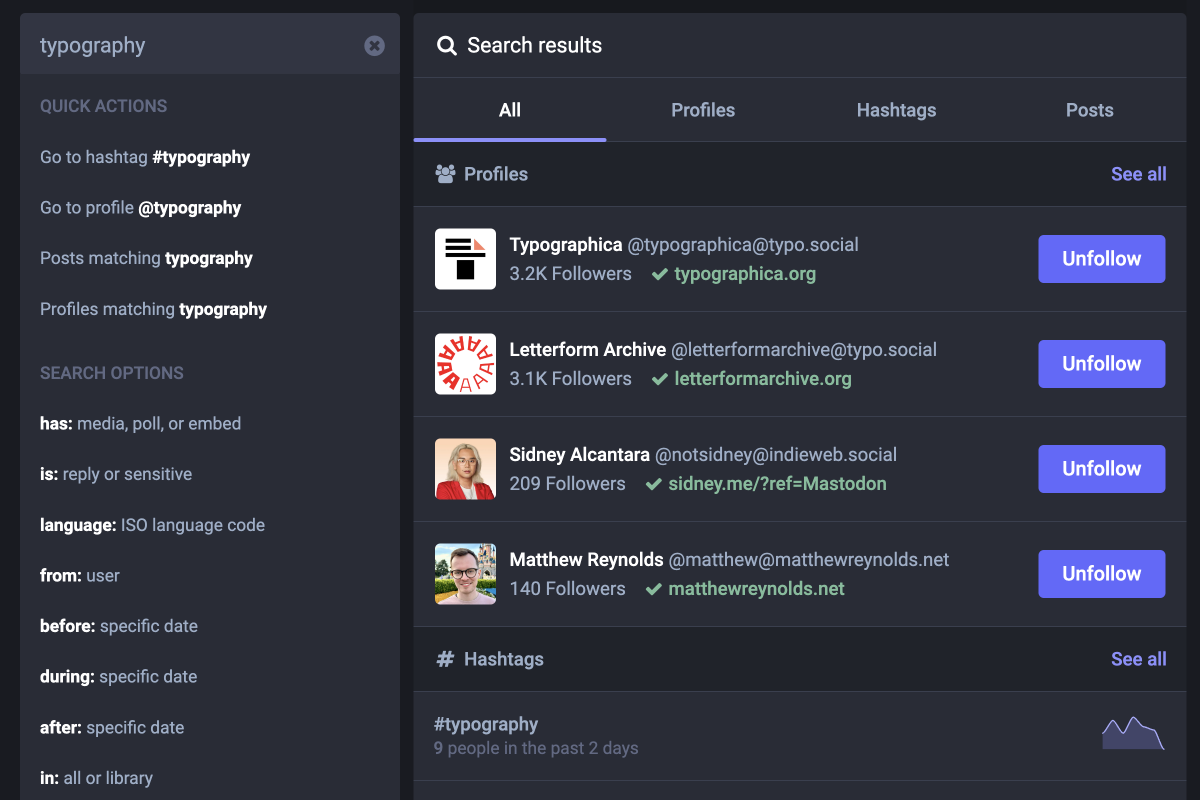 Fig 2: full-text search
Fig 2: full-text search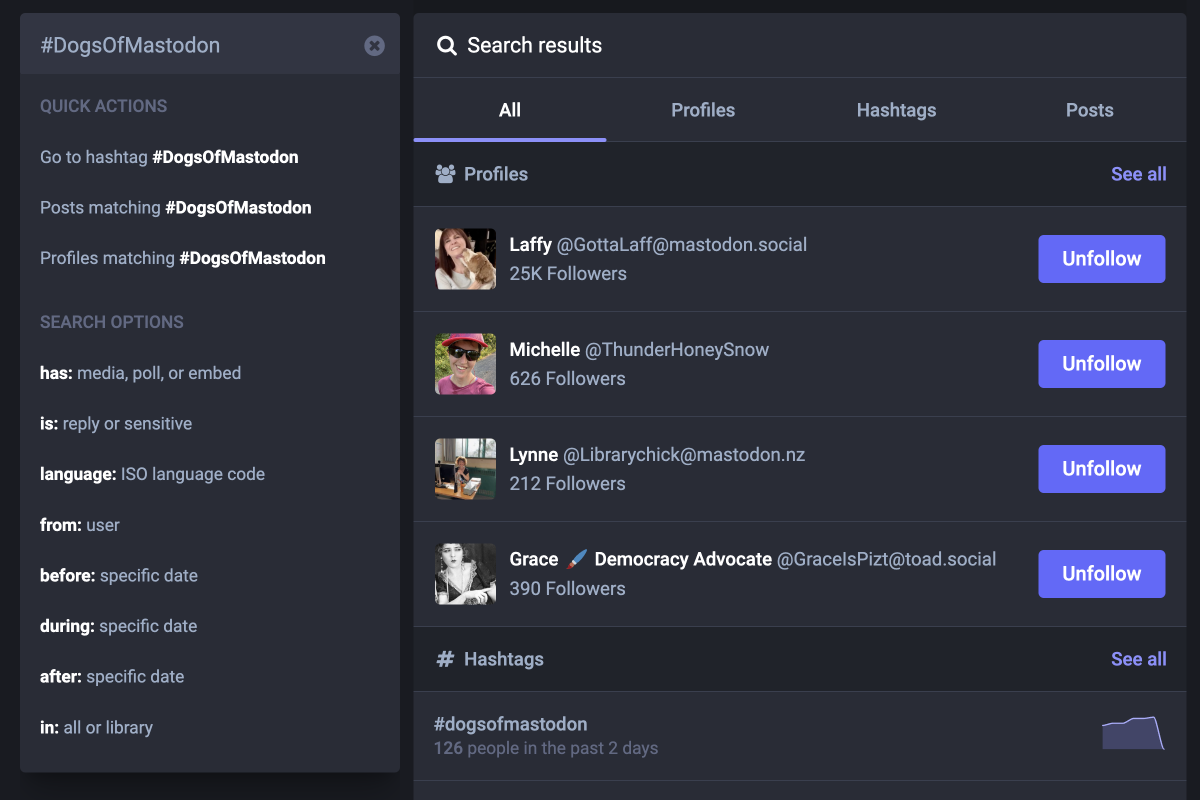 Fig 3: hashtag search
Fig 3: hashtag search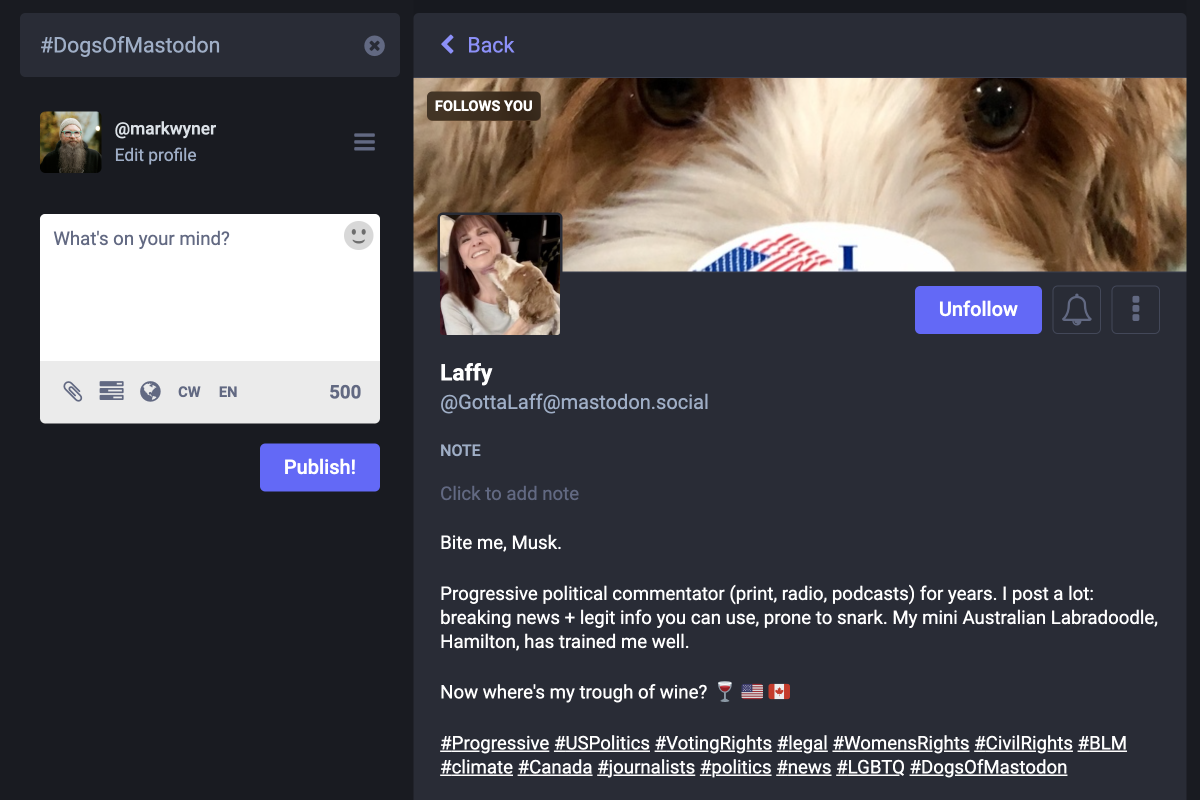 Fig 4: profile match
Fig 4: profile match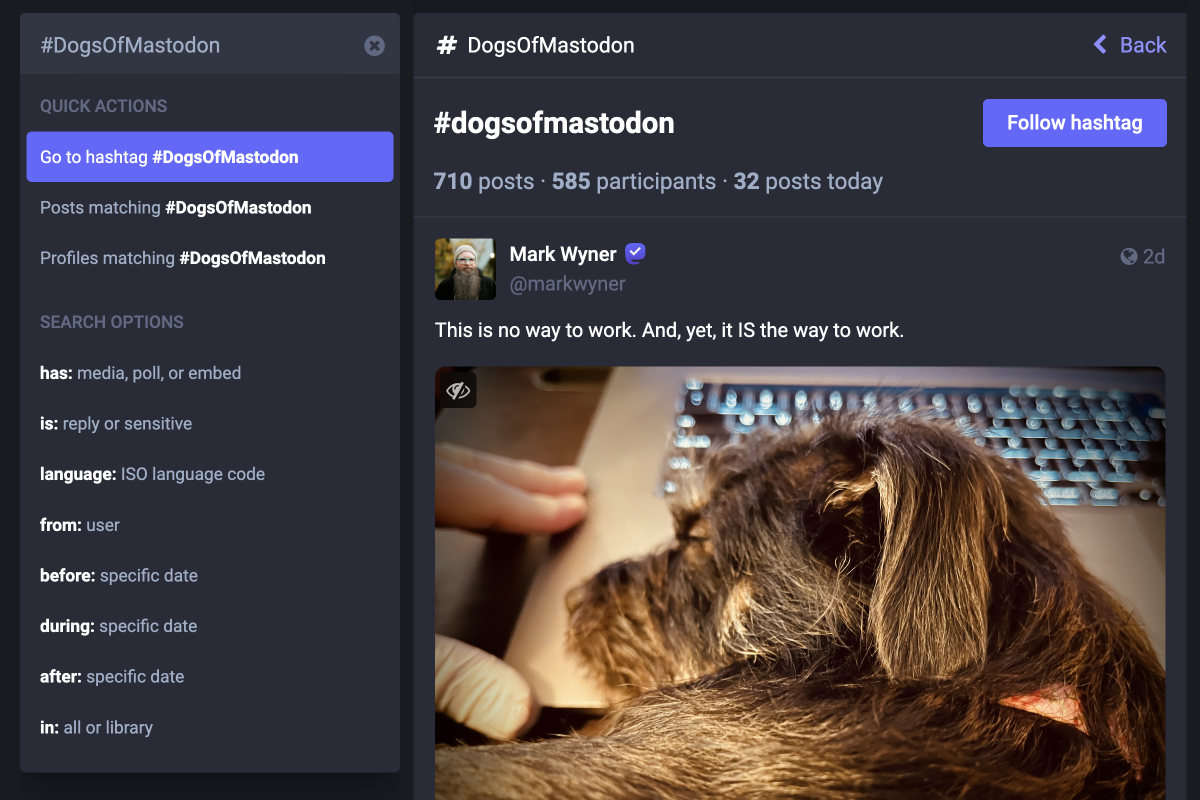 Fig 5: results target
Fig 5: results target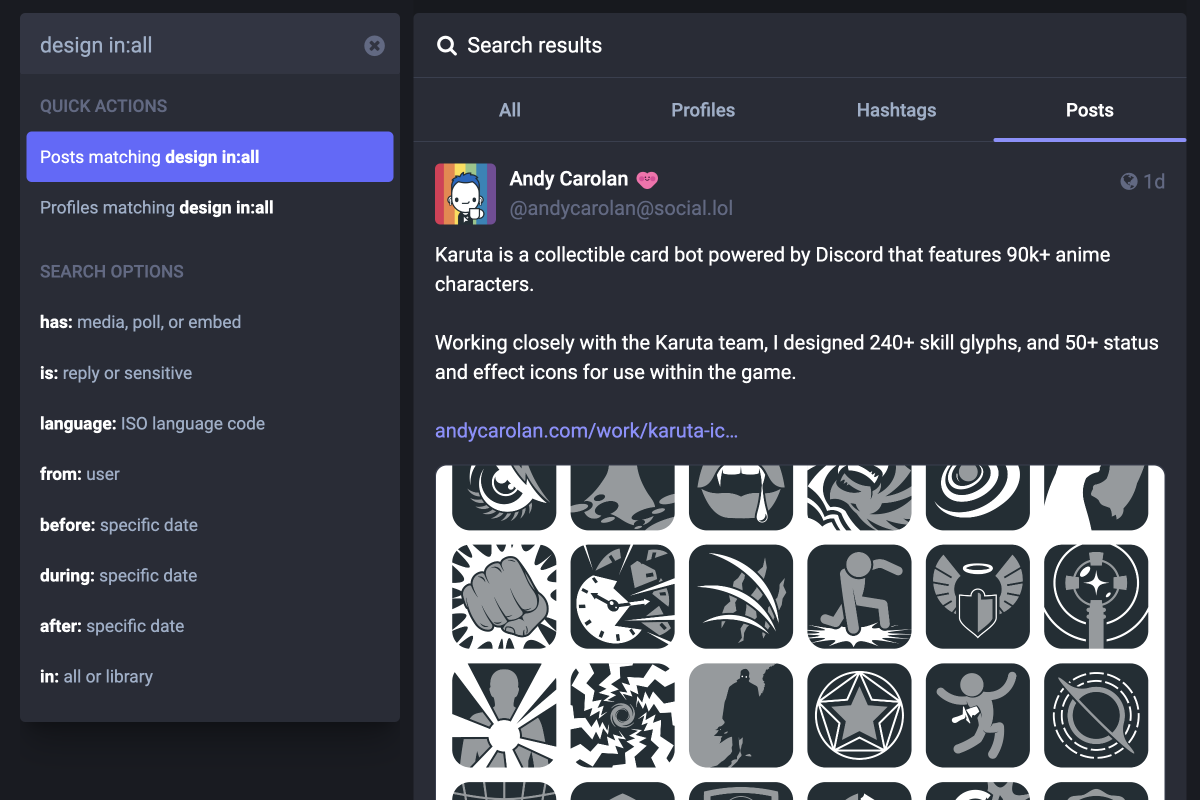 Fig 6: in all
Fig 6: in all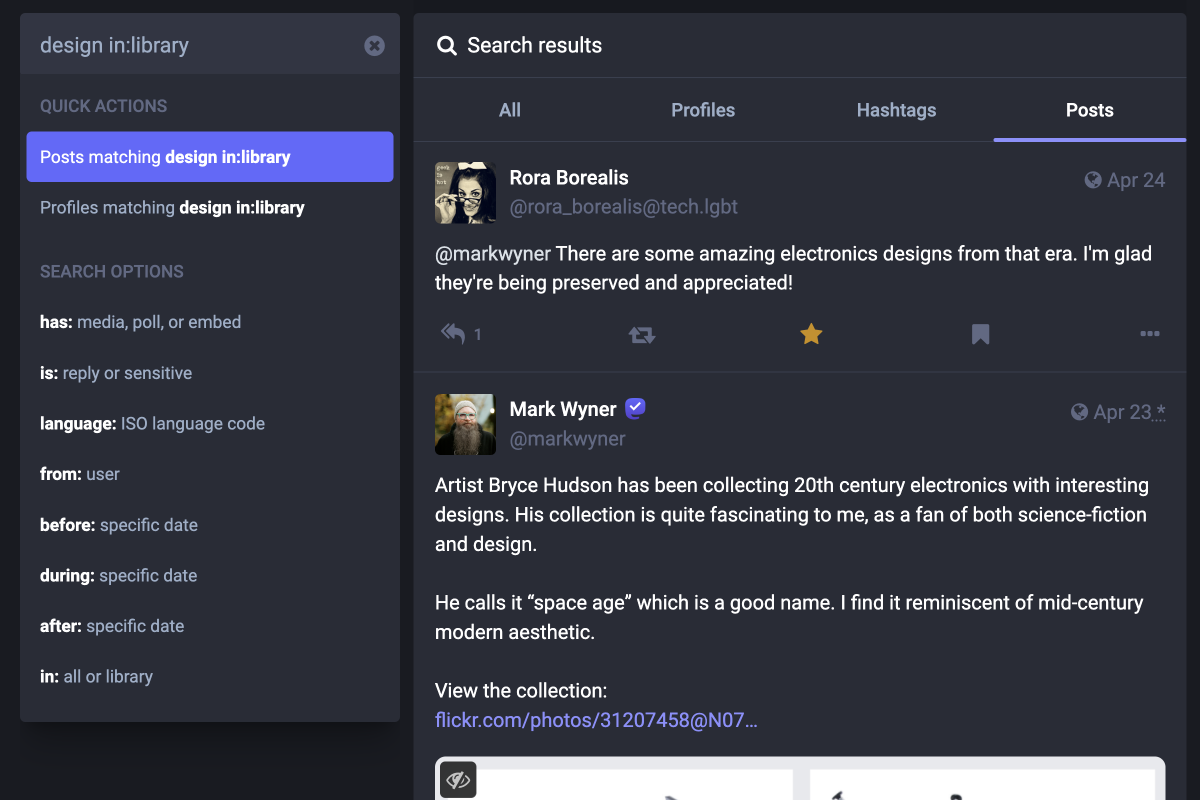 Fig 7: in library
Fig 7: in library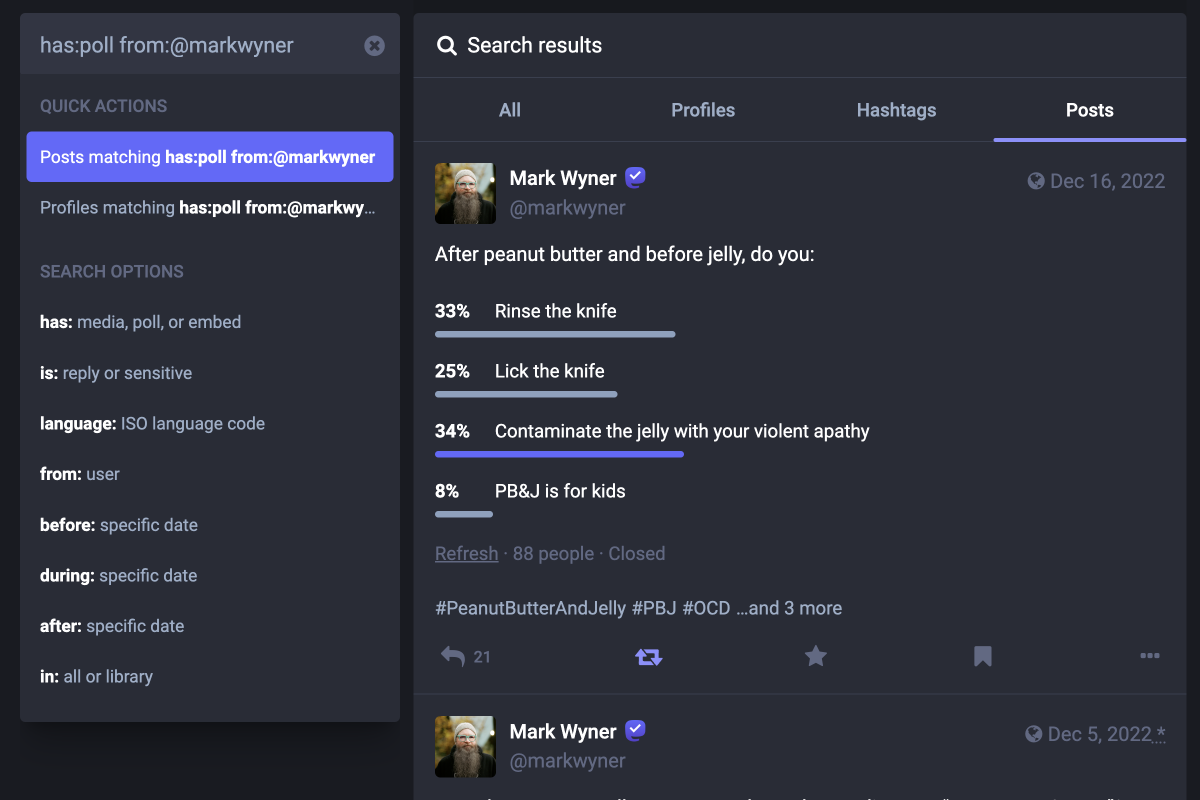 Fig 8: mix and match
Fig 8: mix and match I’m Mark Wyner, an activist, dad, husband,
I’m Mark Wyner, an activist, dad, husband,