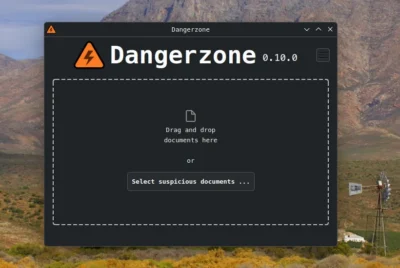
Dangerzone — an open source app to safely open suspect PDFs, office docs, or images
Dangerzone works like this: You give it a document that you don’t know if you can trust (for example, an email attachment). Inside a sandbox, Dangerzone converts the document to a PDF (if it isn’t already one), and then converts the PDF into raw pixel data: a huge list of RGB colour values for each page. Then, Dangerzone takes this pixel data and converts it back into a PDF.
It has been independently audited and apart from the obvious use by journalists and similar professions, even every day users can be most often targeted by attachments that carry payloads of malware. This is exactly how bad actors bypass firewalls, and secure messengers like Signal.
I would not necessarily put every document I receive through this process as it does at least double or triple the size of the file (converts every page to an image). But from anyone you don’t know, this is a useful tool to have ready to use. Everything is processed locally on your machine, and it will install on Linux, Windows, and macOS.
See dangerzone.rocks/category/unca…
#Blog, #opensource, #security, #technology
like this
csa and N. E. Felibata 👽 like this.
N. E. Felibata 👽 reshared this.
csa
•Danie
•